
Just when you think you can’t have it all, you can.
The problem
There are some EC2 instances in your AWS account that you can't access: SSH is turned off, there is no Instance Connect access, and there's no SSM agent installed. You’d like to scan them for misconfigurations and vulnerabilities, but how?
The solution
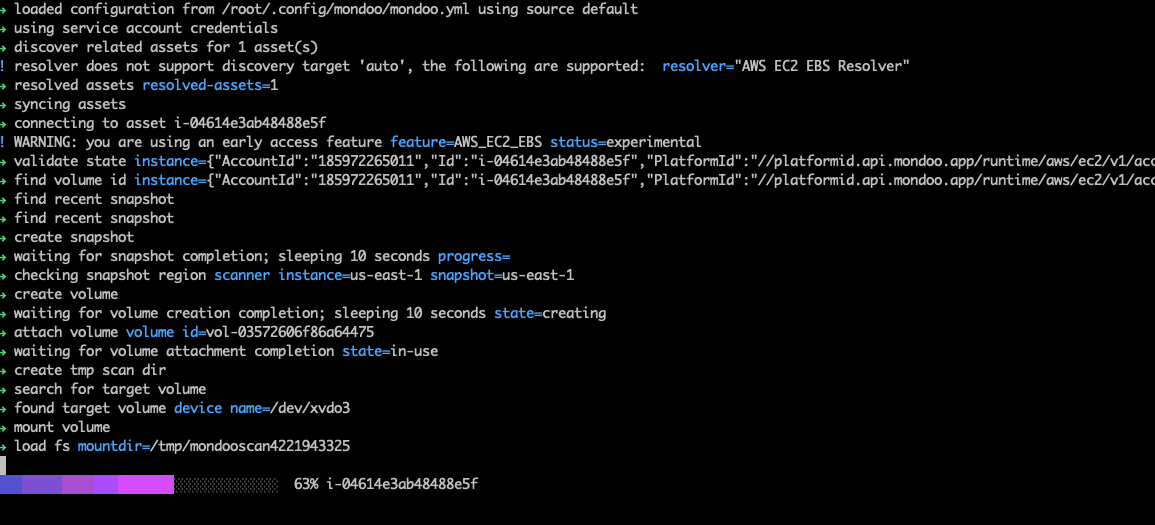
Use open source cnspec side scanning! 🎉 cnspec knows how to create a snapshot of the target EC2 instance, create a volume from that snapshot, and scan that volume for misconfigurations and vulnerabilities.
But how?
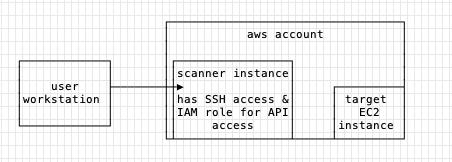
There are a few steps here, but the idea is simple: create the scanner instance ( an instance that has AWS API access and is accessible via SSH), install cnspec, and scan away! The scanner instance is responsible for finding the target volume, snapshotting it, and scanning that target volume.
Step one: Create the scanner instance in the same AWS account and VPC as the target instance. Ensure you can SSH to that instance.
Step two: Create a new role that you will attach to the scanner instance. Attach these two AWS-managed policies to the role: AmazonSSMManagedInstanceCore AmazonSSMReadOnlyAccess
Create a custom policy with these permissions and add it to the role:
"Statement": [
{
"Effect": "Allow",
"Action": [
"ec2:AttachVolume",
"ec2:DetachVolume",
"ec2:DeleteVolume",
"ec2:DeleteSnapshot"
],
"Resource": "*",
"Condition": {
"StringEquals": {
"aws:ResourceTag/Created By": "Mondoo"
}
}
},
{
"Effect": "Allow",
"Action": [
"ec2:CreateSnapshot",
"ec2:CreateVolume",
"ec2:CopySnapshot",
"ec2:CreateTags",
"ec2:DescribeInstances",
"ec2:DescribeVolumes",
"ec2:DescribeSnapshots",
"kms:Decrypt",
"kms:ReEncryptTo",
"kms:GenerateDataKeyWithoutPlaintext",
"kms:DescribeKey",
"kms:ReEncryptFrom"
],
"Resource": "*"
},
{
"Effect": "Allow",
"Action": "kms:CreateGrant",
"Resource": "*",
"Condition": {
"Bool": {
"kms:GrantIsForAWSResource": true
}
}
}
]
Step three: SSH to the scanner instance. Follow the instructions in the AWS console for this, something like ssh ec2-user@54.226.221.203 -i ~/.ssh/key.pem
Step four: Install cnspec on the scanner instance: bash -c "$(curl -sSL https://install.mondoo.com/sh/cnspec)"
Step five: Scan the target instance from the scanner instance sudo cnspec scan aws ec2 ebs i-04614e3ab48488e5f
Do more
Scan more instances, snapshots, and volumes. You can use the same scanner instance you just created for all the scans:
sudo cnspec scan aws ec2 ebs snapshot SNAPSHOT-ID
sudo cnspec scan aws ec2 ebs volume VOLUME-ID
References


