
Welcome to the May 2022 recap of Mondoo releases.
We hit a major milestone in May: Mondoo version 6! For important information about changes in the release, see the Mondoo 6 Release Notes.
We have a lot of exciting changes to share from our work in May:
Kubernetes custom resources support in MQL
New CI/CD views and improved CI/CD integration
Command line interface improvements
Providers in the Mondoo CLI scan
EU region support
AWS integration improvements
Mondoo in the GitHub Marketplace
New asset views
We’ve enhanced the way we visually present the individual assets in your fleet. To explore the new user experience, select any asset.
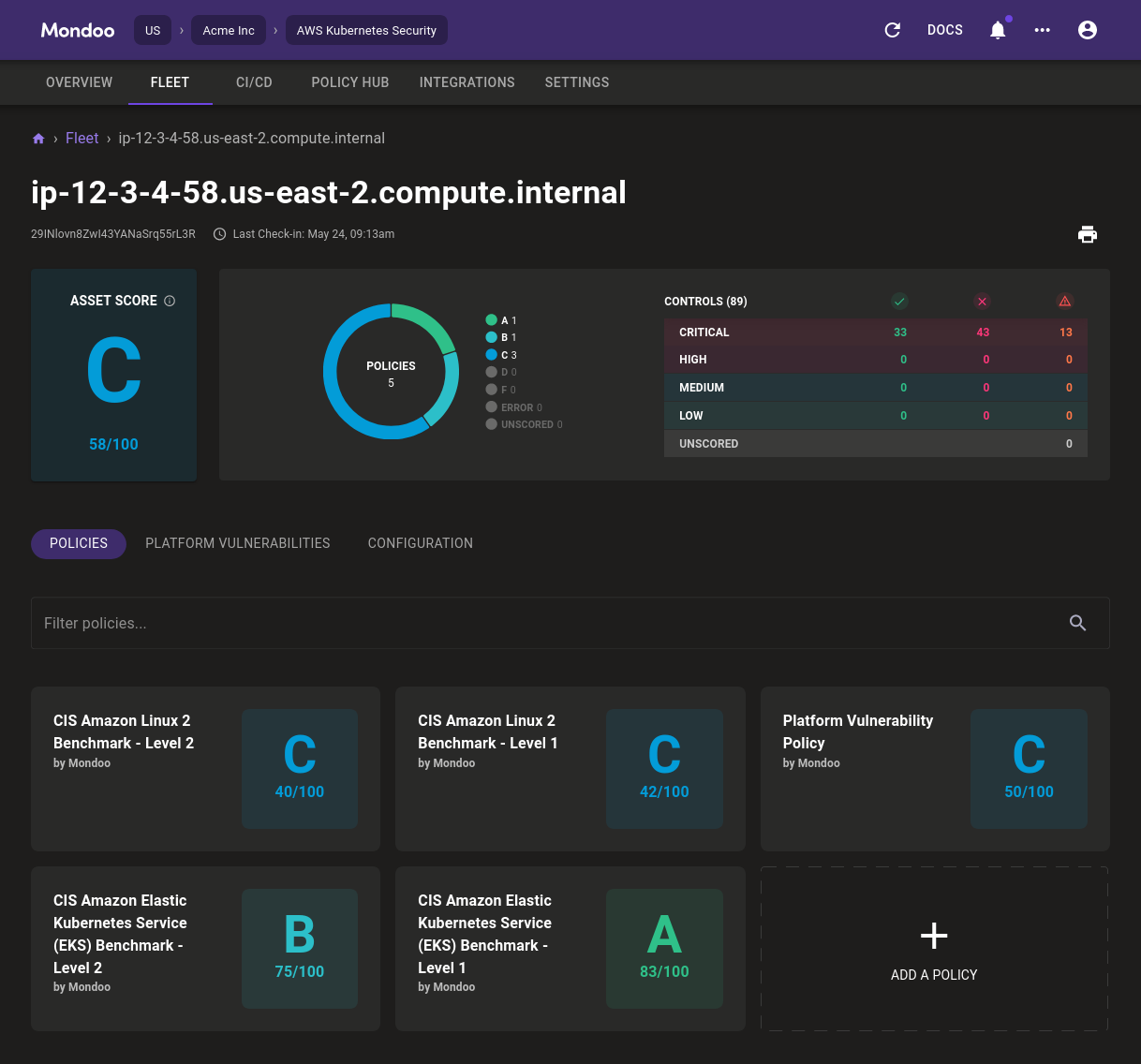
Mondoo now provides a comprehensive overview of the asset’s status at a glance. You see the overall score on the left and, beside that, the score distribution across policies. On the right is a distribution of controls (rules in a policy), arranged by priority. This provides a quick assessment of the critical controls that either fail or have errors.
Below the asset summary are tabs to explore the asset in detail. We’ve made exciting changes to two tabs in the past month: Policies and Platform Vulnerabilities.
Policies tab
The first tab (shown above) shows an overview of all policies that Mondoo applies to this asset and the current summary scores it gives the asset. You can drill down into any of these policies to see a detailed breakdown of controls and their statuses.
Platform Vulnerabilities tab
For most assets, Mondoo provides a detailed and interactive vulnerability analysis.
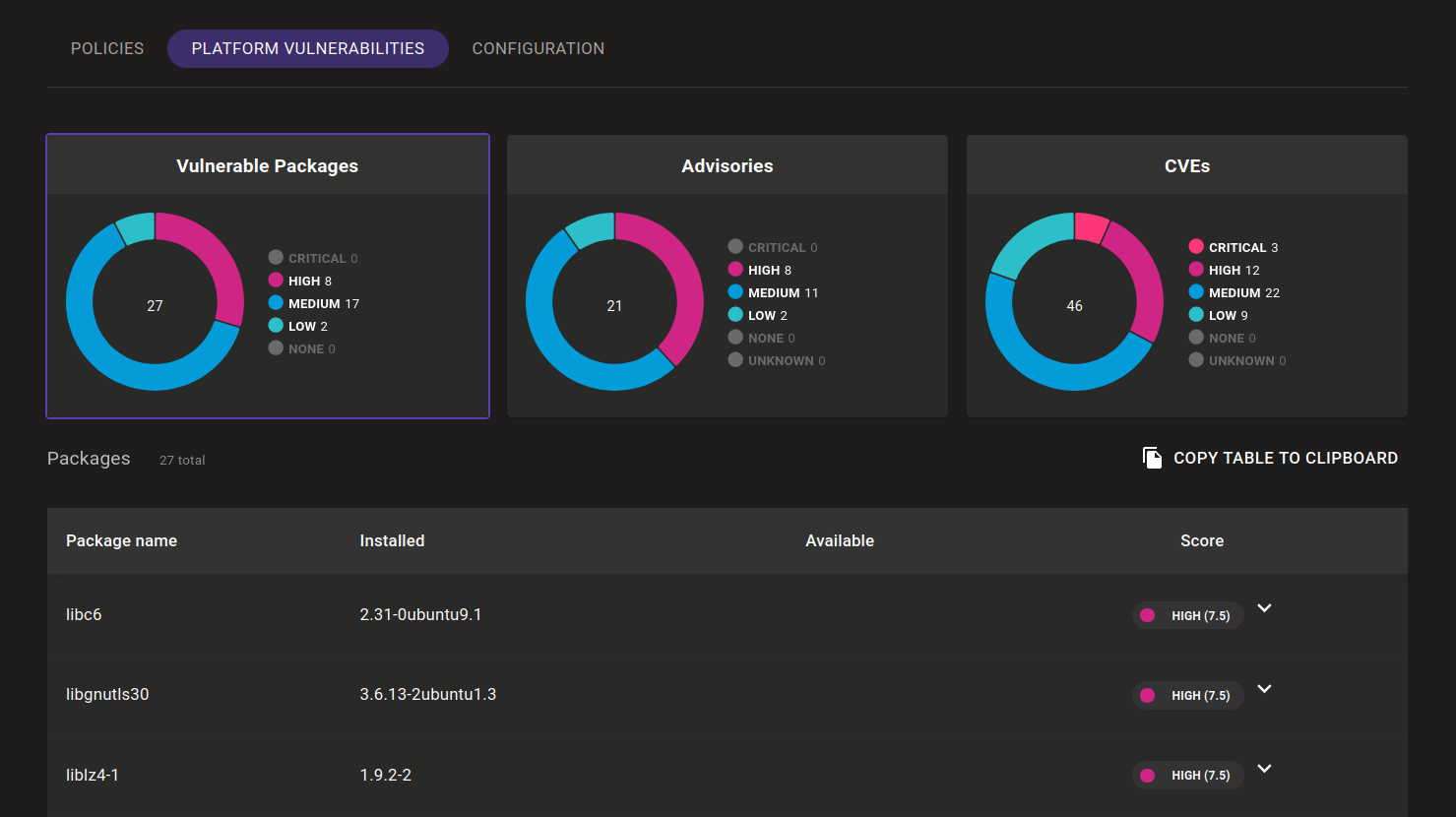
Select the packages, advisories, and CVEs views, which provide different perspectives on current vulnerabilities:
- Vulnerable Packages lists the most impactful components you need to update in order to fix these vulnerabilities.
- CVEs gives security specialists a breakdown of all the detected vulnerabilities.
- Advisories shows the vendor announcements that connect the packages and vulnerabilities.
Right now, the Mondoo team is developing more asset view changes that will help you prioritize issues and take action. Stay tuned!
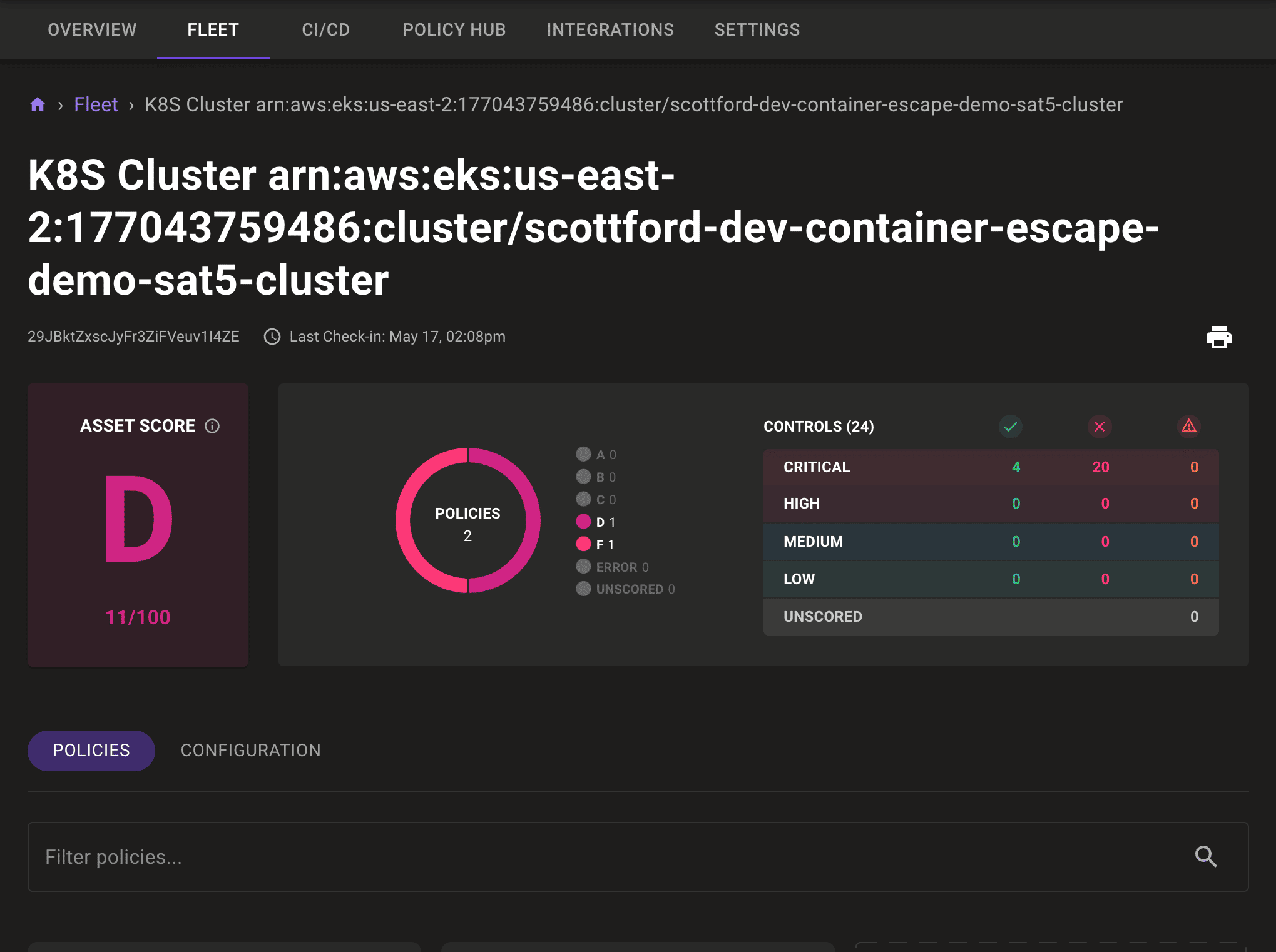
Kubernetes integrations
With the Mondoo Kubernetes Operator, you can now continuously validate your deployed workloads and assess the configuration and security of the nodes running your kubelets. When you couple this with the Mondoo Admission Controller and Mondoo's support for scanning Kubernetes manifests in the CI/CD pipeline, you have a complete solution for securing Kubernetes from commit to production.
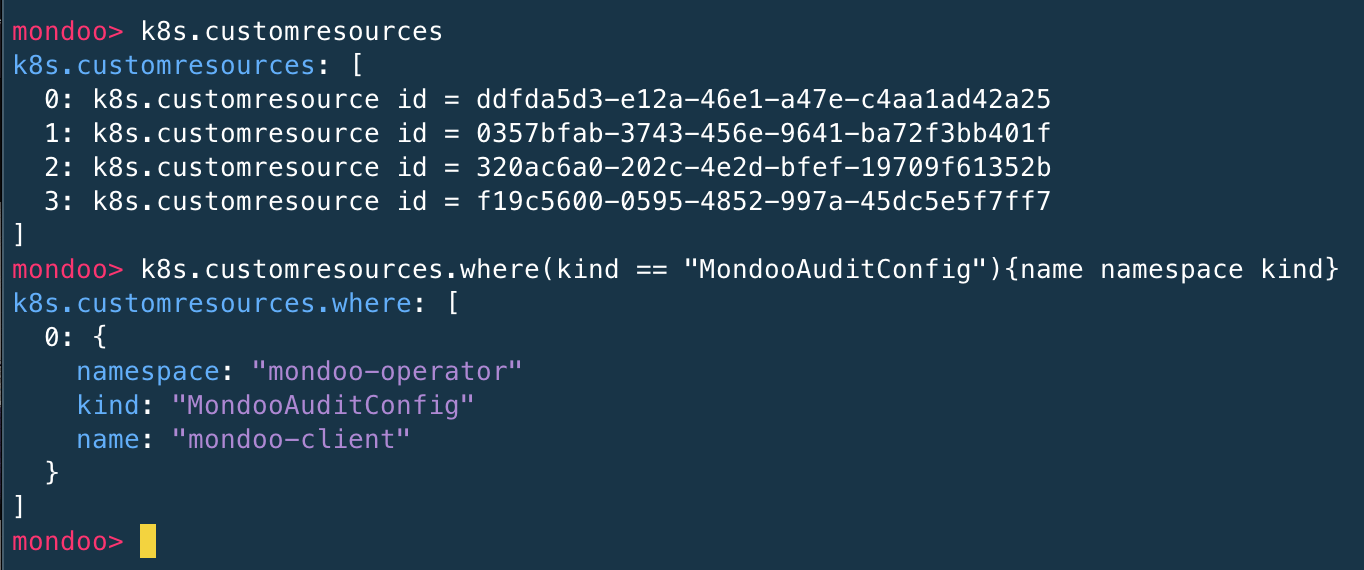
Kubernetes custom resources support in MQL
We’ve made Kubernetes custom resources available in MQL. These make it easier to inspect Kubernetes installations in MQL. Find them under the k8s.customresource keyword.
New CI/CD views and improved CI/CD integration
Many of our May enhancements focus on integrating Mondoo with your CI/CD flow.
New CI/CD views
To help you better visualize scans of CI/CD pipelines, we've added new, specialized views to the Mondoo Console. Of course, Mondoo already lets you scan infrastructure artifacts during the build process, such as Kubernetes manifests, Terraform code, and Docker images. But now you can use Mondoo to compare different builds and branches as well.
Check out the official documentation and get started today!
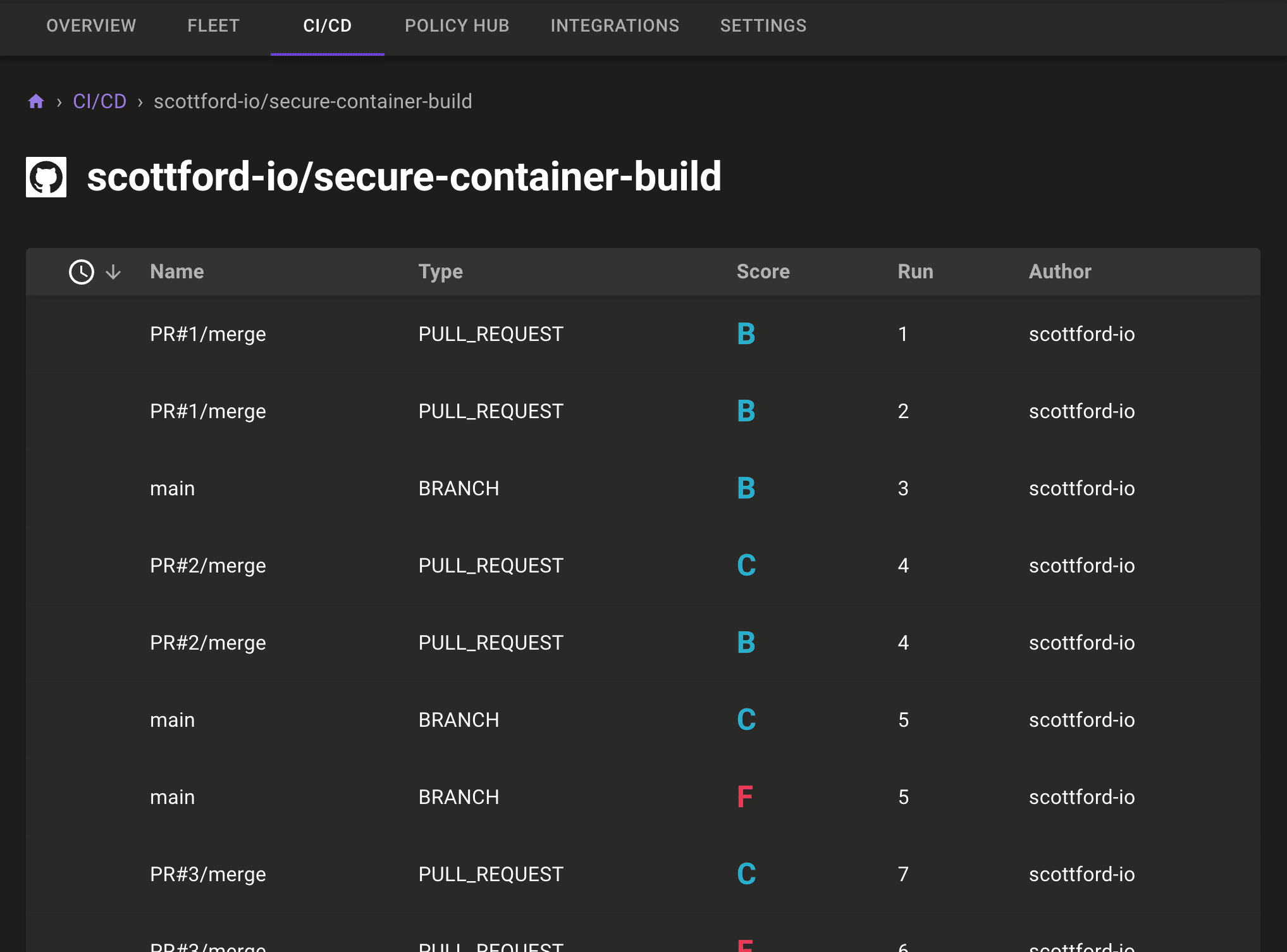
Automatic client detection
We now automatically detect the Mondoo client running in CI/CD environments. Once we detect it, we collect more contextual information about the run, such as the repository, PR/MR number, and Git reference. This allows CI/CD runs to automatically show up in the CI/CD tab, where you can explore more details.
Today, we support this feature for GitHub, GitLab, and Kubernetes out of the box. We are expanding to other systems soon, so stay tuned!
Streamlined exit codes
We’ve improved how Mondoo scan results affect CI/CD pipelines. Previously, unless they achieved perfect scores (A+ with a score of 100), Mondoo scans finished with a non-zero exit code. This caused the pipeline to fail, even with only minor issues. Now, by default, every Mondoo returns an exit code of 0 when a scan is successful. Both As and Fs show a successful run.
With the previously introduced --score-threshold you can customize this behavior to fail the execution (exit code 1) whenever the score falls below your chosen threshold. For example, this command fails all scans that result in an F (score below 10):
mondoo scan --score-threshold 10
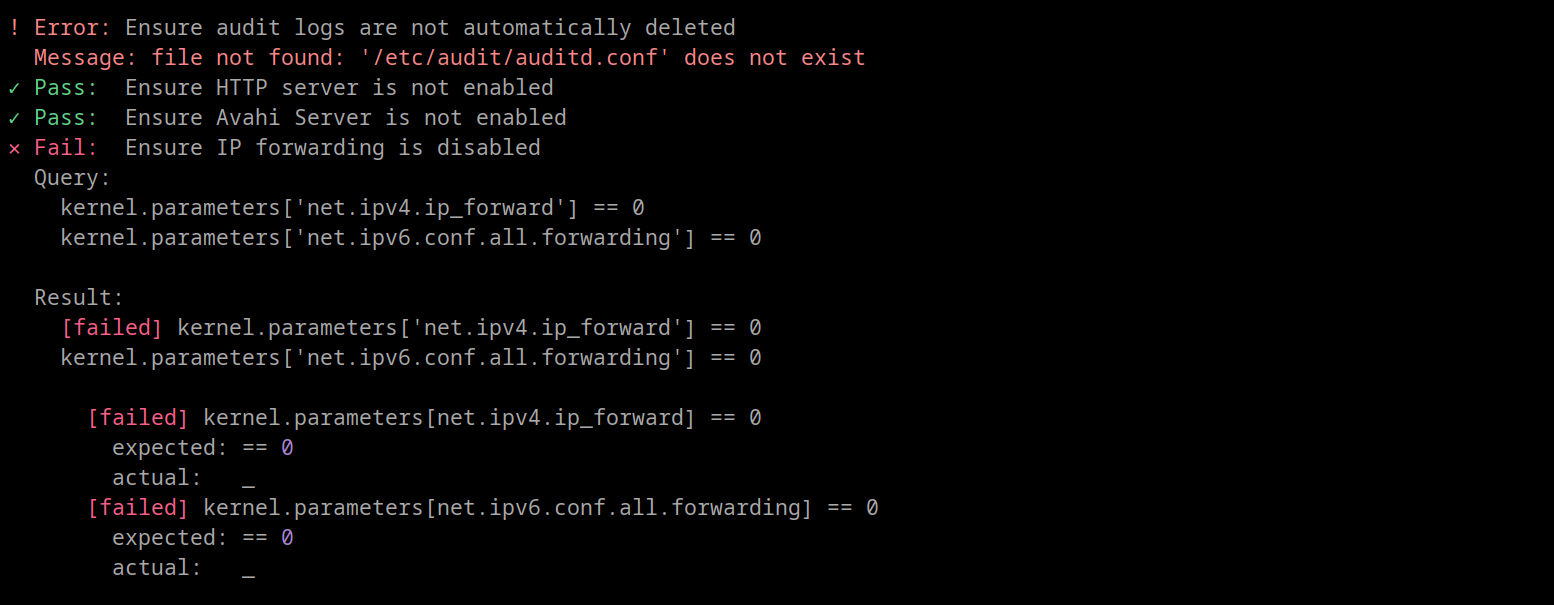
Command line interface improvements
We’ve made big changes to our CLI in response to customer feedback: We built a new default report output, and we’ve made the mondoo scan command easier to use.
Providers in the Mondoo CLI scan
Mondoo can scan many different types of targets, from your local machine, to remote machines via SSH or WinRM, to cloud systems like AWS or Azure, and even arbitrary APIs. We’ve updated the scan command to make it easier to specify the scan target: mondoo scan
You no longer need the -t or --connection options. These are some examples using different providers:
mondoo scan local
mondoo scan ssh user@host
mondoo scan container b62b
mondoo scan container image ubuntu:20.04
mondoo scan aws
For a list of all available providers and detailed help on the scan command, type:
mondoo scan -h
CLI report overhaul
We redesigned our CLI reports with developers and operations experts in mind. We first print a list of controls and data queries, then list vulnerabilities, and finish with a short summary. We removed pagination based on feedback from customers like you. The default report is also much more compact:
mondoo scan local
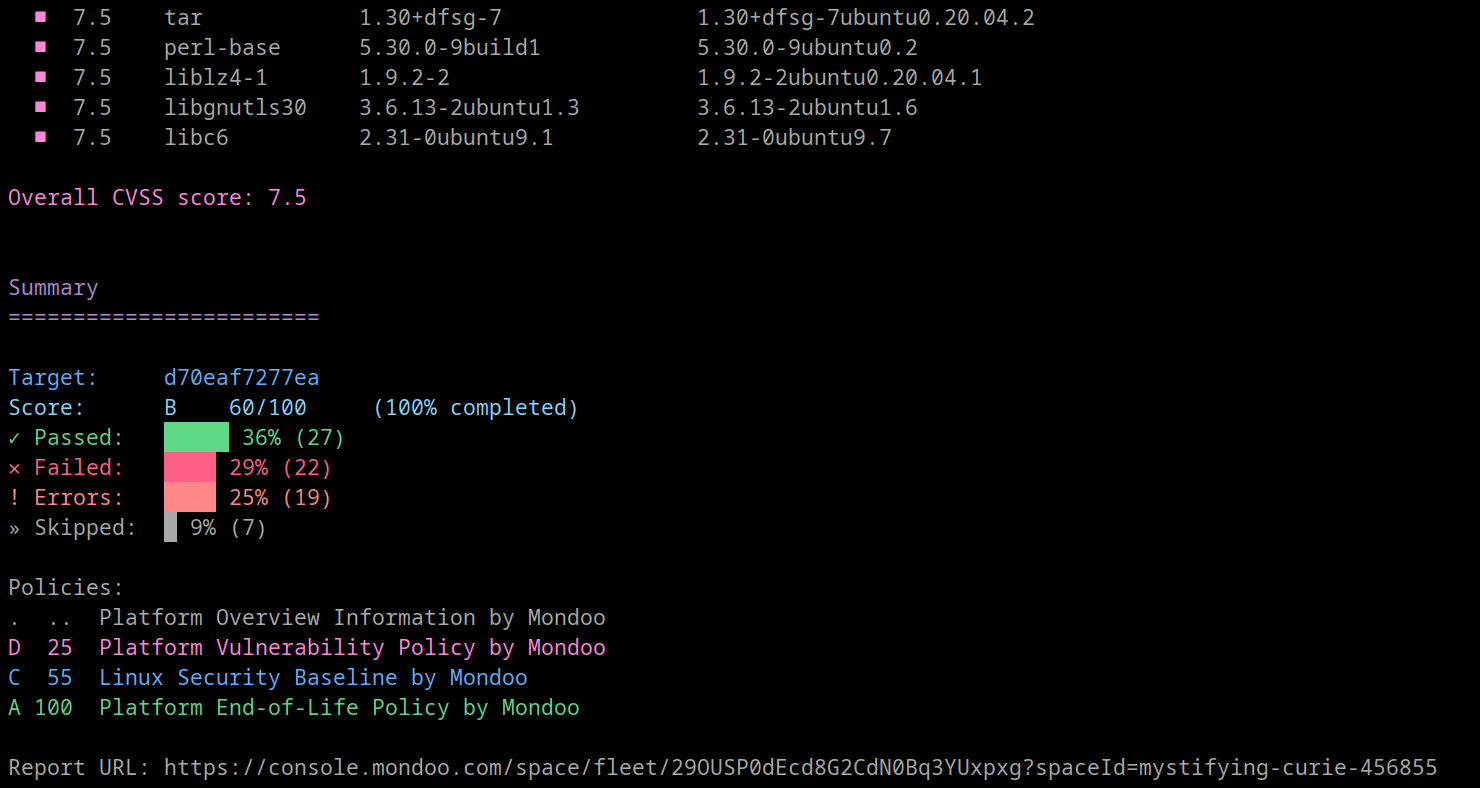
For more information about individual controls, use the full formatter:
mondoo scan local -o full
The legacy default report, which we designed for auditors and security experts, is still available:
mondoo scan local -o full
Output formats include JUnit, JSON, CSV, and YAML. You can list them all:
mondoo scan -o help
EU region support
Many of our customers in the EU are subject to local regulatory requirements. They need the data storage and processing that Mondoo performs on their behalf to occur in Europe. To meet this need, Mondoo has added new cloud infrastructure in the EU.
When you create a new organization, you can choose whether to locate it in the US region or EU region. All data created and processed in the EU region happens on servers located in data centers within the EU.
To create or access an organization in a different region, use the US / EU region menu:
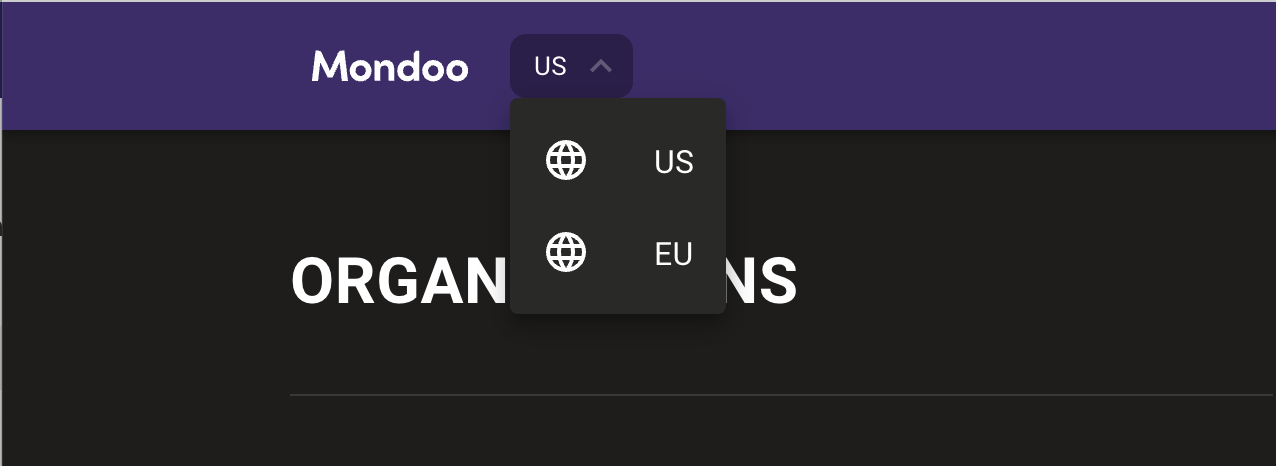
Mondoo keeps all of the data stored and processed in the two regions completely separate. You can't move assets between the two regions, nor can you share data between the two in any way.
AWS integration improvements
We’re excited to release the Mondoo AWS Organization integration, which allows you to set up AWS integrations across your entire AWS Organization or organizational unit.
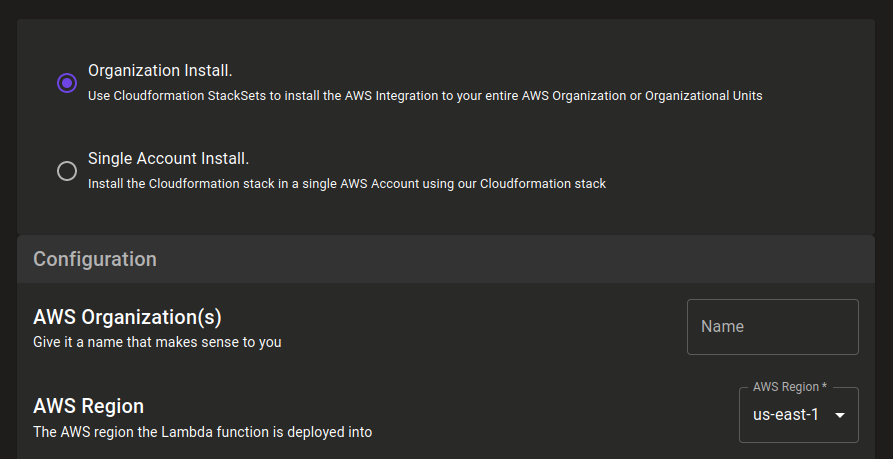
We previously only supported single account installations. With this change, you can use AWS CloudFormation StackSets to install the integration across all accounts in your AWS Organization. This automatically installs the integration to all new accounts added to that AWS Organization.
Furthermore, we now display the number of EC2 Snapshots, CloudWatch LogGroups, Lambda Functions, Config Recorders, and EKS clusters on your AWS integration page:
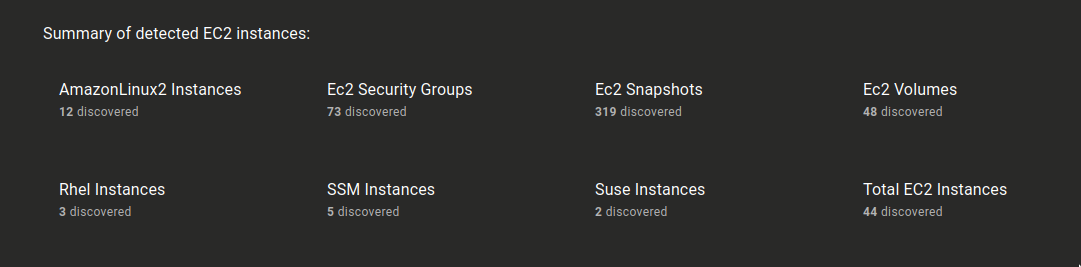
This discovery is only the beginning; we have exciting plans for the exploration of your fleet!
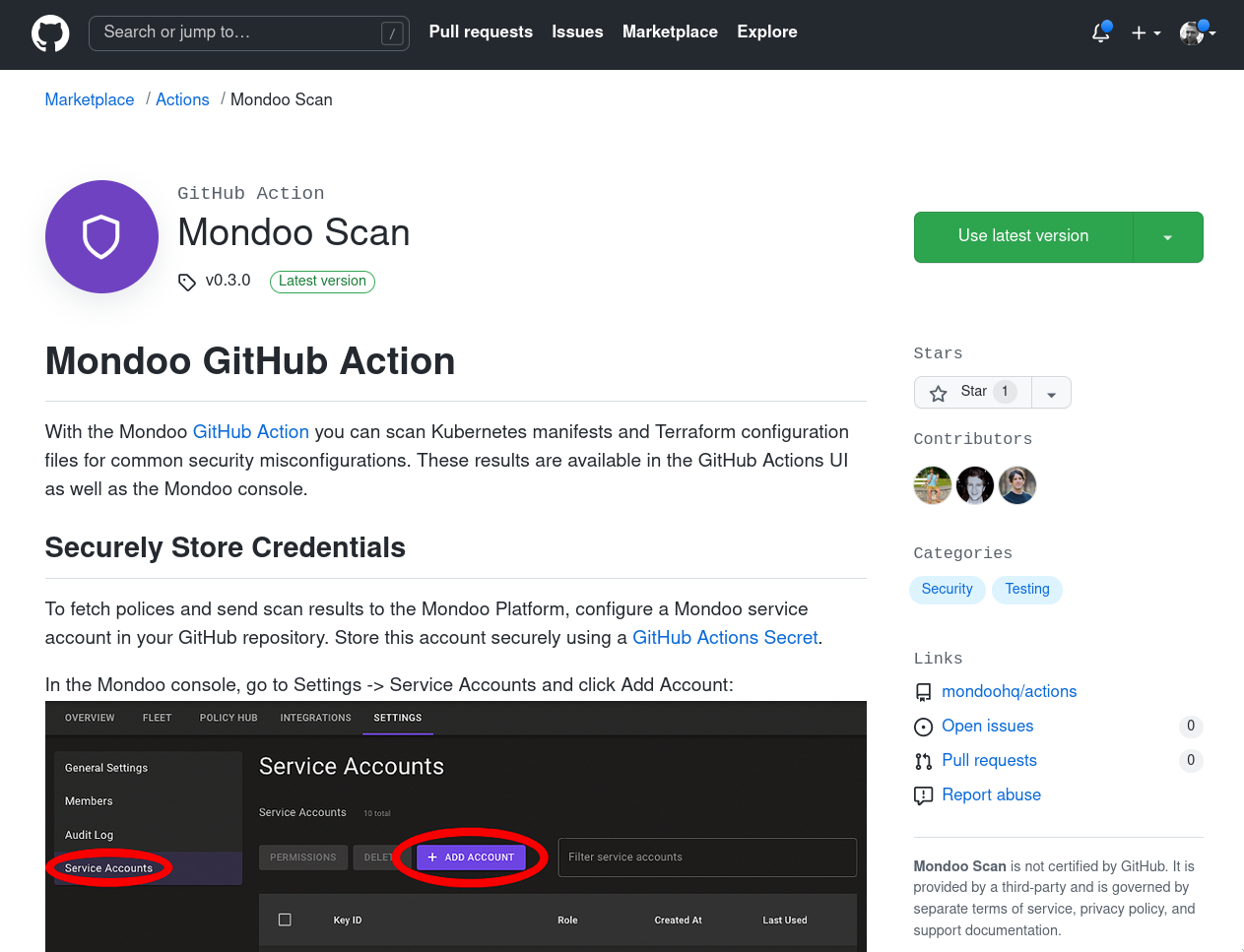
Mondoo in the GitHub Marketplace
To go with our new GitHub CI/CD views, Mondoo is now available as an Action in the GitHub Marketplace. Use Mondoo with Github Actions to scan Kubernetes manifests, Terraform configuration files, and Docker images. See examples and full setup instructions on our page in the Github Marketplace.
MQL improvement
MQL now supports variables across blocks. This enhancement makes many queries easier to write.
Here is a simple example:
aws.dynamodb.tables {
x = region
aws.dynamodb.
limits.
where(region == x) {*}
}
In this example, we define a new variable x and set its value to the region of the table. We can then use the variable to access the limits entry that matches this region. Previously this was not possible, since both fields had the same name (region) and variables weren’t accessible across blocks.
Policy updates
The Center for Internet Security (CIS) officially certified the Mondoo Ubuntu 20.04 Level 1 and Level 2 CIS Benchmarks. See the Mondoo page at cissecurity.org for a complete list of our CIS-certified benchmarks, and stay tuned for more certifications in the coming weeks.
In addition, we updated these policies:
- Linux Security Baseline by Mondoo
- Kubernetes Application Benchmark by Mondoo
We also updated the detection of EOL dates and package vulnerabilities for Red Hat Linux 9 and AlmaLinux 9.
You can find all of these policies in your Policy Hub: select Add Policies




